Forensic Software: Everything You Need to Know About Computer Forensics
When the average person hears the phrase “computer forensics” or “forensic computing”, an image of a shadowy figure wearing mirrored glasses immediately comes to mind. But is it an accurate representation of what computer and digital forensics are really all about? It’s not, as you’ll soon find out in this article.

Even though the same tools used by a real computer forensic specialist are used by his or her underground counterpart, the essence of digital forensics is data recovery and preservation. If you ever used a computer data recovery tool, such as Disk Drill, to recover lost files from your computer, you already have a rough idea about one aspect of the forensic computer science and the life of a computer forensic investigator. In this article, you are going to learn the rest.
Computer Forensics Definition
Techopedia defines computer forensics as “the process of uncovering and interpreting electronic data”. The main goal of this process is to “preserve any evidence in its most original form while performing a structured investigation by collecting, identifying and validating the digital information for the purpose of reconstructing past events”.
In other words, digital forensics is a branch of the same old forensic science that you know from old crime TV shows. You know how they usually go: a horrendous murder is committed. Police officers arrive at the scene with the chief investigator leading the pack in his Ford Galaxie 500. As soon as they step out their vehicles, somebody yells “Don’t touch anything! We need every piece of evidence we can find”.
Back in the day, such evidence would often be someone’s diary or a fingerprint on a glass of water. These days, it’s digital metadata, log files, IP addresses, and leftover chunks of ones and zeros. Some of the very first digital crimes can be traced back to the late 1970s and early 1980s. In those days, computer security and privacy were the subjects of interest to only a very small group of geeks and innovators.
A major turning point occurred in 1978, with the 1978 Florida Computer Crimes Act, which recognized the first computer crimes in the United States and included legislation against unauthorized deletion or modification of computer data. Other acts, such as the US Federal Computer Fraud and Abuse Act of 1986 and the British Computer Misuse Act of 1990, followed soon after that.
Before the arrival of the new millennium, the discussion still revolved mostly around recognizing computer crimes as serious threats to personal, organizational, and national security. Since 2000, a new need for standardization arose, leading to the production of “Best practices for Computer Forensics” and the publication of ISO 17025 by the Scientific Working Group on Digital Evidence (SWGDE).
These standards and guides helped established a set of best practices for computer forensic specialists to follow and ignited computer forensics companies to produce capable forensic data recovery software solutions that would be able to meet the complex demands of the modern age.
The typical forensic process has several distinct stages: the seizure, forensic acquisition, analysis, and the production of a report based on the collected data. There are special free forensic software tools as well as paid forensic tools for each stage. A list of digital forensics tools can be found later in this article.
Sub-Branches of Computer Forensics
Computer forensic specialists either deal with the private or the public sector. With the public sector, their work is usually to support or refute a hypothesis before criminal or civil courts. The bread and butter of private sector forensic investigators are corporate investigations and intrusion investigations.
As the complexity of modern technology increases, computer forensic specialists often focus on one or a number of sub-branches of digital forensics, to gain expert-level knowledge. Digital forensics is typically divided according to the type of devices involved. The major branches are computer forensics, mobile device forensics, network forensics, forensic data analysis, and database forensics.
The one branch that has seen the most growth over the past few years is mobile device forensics. As people replace laptops and desktop computers with smartphones and tablets, the need for cell phone forensic software capable of forensic cell phone data recovery rises dramatically.
Computer Forensic Tools and Equipment
To describe some of many computer forensic tools used by computer forensic investigators and specialists, let’s imagine a crime scene involving child pornography stored on a personal computer. In most cases, investigators would first remove the PC’s HDD and attach with a hardware write blocking device. Such device makes this completely impossible to alter the content of the HDD in any way while allowing investigators to capture and preview the content of the disk.

PROTEGGA USES THE MOST MODERN COMPUTER FORENSIC DETECTION TOOLS
A bit-accurate copy of the disk can be made with a variety of specialized tools. There are large digital forensics frameworks and software solutions, alongside countless smaller utilities. The former group includes Digital Forensics Framework, Open Computer Forensics Architecture, CAINE (Computer Aided Investigative Environment), X-Ways Forensics, SANS Investigative Forensics Toolkit (SIFT), EnCase, The Sleuth Kit, Llibforensics, Volatility, The Coroner’s Toolkit, Oxygen Forensic Suite, Computer Online Forensic Evidence Extractor (COFEE), HELIX3, or Cellebrite UFED.
These large software solutions and forensic suites include a wide range of forensic data services in a single package. However, many professional forensic specialists prefer to build their own customized toolboxes from individual tools and utilities that exactly fit their needs and preferences. The options are plentiful for every stage of the forensic data recovery process, including hard drive forensics and file system forensic analysis.
Data capture can be done with the help of EnCase Forensic Imager, FTK Imager, Live RAM Capturer, or Disk2vhd from Microsoft. Emails are analyzed with tools such as EDB Viewer, Mail Viewer, or MBOX Viewer. Some tools are made specifically to target certain operating systems, while others support multiple platforms. Popular tools for Mac OS X include Disk Arbitrator, Volafox, and ChainBreaker, which parses keychain structure and extracts user’s information. Needless to say that no forensic analyst can be without a sizable assortment of internet analysis tools, including Dumpzilla from Busindre, Chrome Session Parser, IEPassView, OperaPassView, and Web Page Saver from Magnet Forensics.
Features of Professional Forensic Tools
Features of professional forensic tools vary greatly depending on what aspect of forensic analysis they target and what market they are aimed at. Generally, large forensic software suites have to be able to do the following:
- Support hashing of all files, which allows comparative filtering
- Full disk hashing to be able to confirm that the data has not changed (typically one tool is used to acquire and another is used to confirm the disk hash)
- Exact pathway locators
- Clear time and date stamps
- Have to include an acquisition feature
- Search and filtering of items
- The ability to load iOS backups and parse their data
Compared to law enforcement agencies, corporations are usually not concerned with volatile RAM captures. They want to acquire the evidence for private investigation and/or turn over to Law Enforcement. They are also usually not interested in previewing ability.
Major Forensic Software Providers
The field of forensic software analysis is filled with forward-thinking innovators and prolific, existing software companies that are ready to expand their operation. Large forensic software providers tend to appear at large industry gatherings, such as the High Tech Crime Investigation Association Conference, but there are many of these conferences across North America.
Let’s take a look at some of the most prolific forensic software providers and their products.
BlackBag Technologies

BlackLight by BlackBag is the premiere Mac Forensic Tool on the Market right now and costs approximately $2600. BlackLight started 5 years ago, developing a Mac-only forensic tool. It has now become a good Windows examination tool as well. It will analyze all iOS devices as well as Android. However, it is not capable of analyzing BlackBerry devices. One thing that Blacklight doesn’t do on its own is the forensic acquisition of bit for bit clones. They have an additional tool called MacQuisition.
MacQuisition runs a stripped down version of iOS 10 and costs over $1000 USD because of licensing to Apple. It does a very good job of discovering encryption and can join together fusion drives into one volume.
AccessData https://accessdata.com

AccessData is the leading provider of E-Discovery, Computer and Mobile Device Forensics for corporations, law firms, and government agencies. Their digital forensics solutions include Forensic ToolKit (FTK), which provides comprehensive processing and indexing up front, so filtering and searching are faster than with any other solution on the market.
The company is widely known for their mobile forensics tools, including Mobile Phone Examiner Plus (MPE+) and nFIELD. The former allows mobile forensic examiners to quickly collect, easily identify and effectively obtain the key data other solutions miss. The latter is an agile solution that allows users to perform logical and physical acquisitions of all MPE+ supported mobile devices in just 5 steps.
Guidance Software https://www.guidancesoftware.com
Guidance Software, founded in 1997, develops EnCase Forensic Software, which is a PC-only forensic tool that has been the mainstay of forensics for over a decade. The tool has made the headlines in 2002 when it was used in the murder trial of David Westerfield to examine his computers to find evidence of child pornography, and when French police used EnCase to discover critical emails from Richard Colvin Reid, also known as the Shoe Bomber.
EnCase Forensic Software is capable of acquisitions, hard drive restoration (cloning bit for bit and make a cloned HDD), complete a comprehensive disk-level investigation, and extensive reporting, among many other things.
Magnet Forensics https://www.magnetforensics.com

Developed by a former police officer and programmer, Magnet Forensics is a complete digital investigation platform used by over 3,000 agencies and organizations around the world. Originally, it started as an Internet-only carving tool but has now expanded to become a full-fledged forensic suite. Magnet Forensics can make physical data acquisitions of phones where possible (most Android and iPhone 4 and below, and BlackBerry). These physical acquisitions can be then loaded into tools such as Cellebrite.
X-Ways https://www.x-ways.net
X-Ways is a relative newcomer to forensics, but the company is quickly becoming popular due to its speed of innovation. Developed by a team of German Engineers, forensic tools from X-Ways do a fantastic job when it comes to disk imaging, disk cloning, virtual RAID reconstruction, remote network drive analysis, remote RAM access, cloud storage access, and more. The downside is that they require considerable experience to use.
Cellebrite https://www.cellebrite.com

A subsidiary of Japan’s Sun Corporation, Cellebrite Mobile Synchronization is an Israeli company that is considered to be the leader when it comes to mobile forensic software. Their premier mobile tool comes with a very high price tag of $12,000 USD and a yearly license around of $4000. With the high price goes a top-notch service that provides deep insight into mobile devices through Cellebrite’s Unified Digital Forensics Platform.
CERT
CERT stands for computer emergency response teams. In the United States, the organization was established in 2003 to protect the nation’s Internet infrastructure against cyber attacks. They have developed several tools used by law enforcement, including CERT Triage Tools. Triage Tools are used to capture RAM and make on-scene acquisitions. The product also includes a GNU Debugger extension called “exploitable” that is able to classify Linux application bugs by their severity. Currently, CERT Triage Tools is being publicly developed on GitHub.
Disk Drill’s Take on Forensic Data Recovery
Disk Drill is a proven data recovery tool that has been successfully used by countless users from all around the world to recover documents, images, video files, and other types of data from a variety of different storage devices.
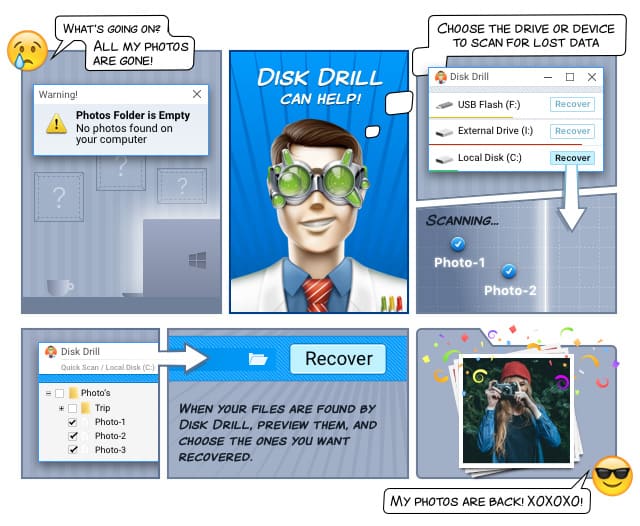
CleverFiles, the company behind Disk Drill, is currently working on a new version of the software, one that will include an assortment of useful forensic tools. This upcoming player on the forensic market is expected to bring to it their signature user-experience characterized by a high degree of user-interface polish and remarkable ease of use.
