Encryption is the process of algorithmically transforming information making it unreadable to unauthorized individuals. It is often employed to safeguard sensitive information such as credit card and bank account numbers. Plain-text data is encoded during encryption and can only be decrypted with a key.

There are a number of encryption algorithms in use that employ either symmetric or asymmetric keys to encode and decode the data. Currently, the Advanced Encryption Standard (AES) algorithm is most often used with 128, 192 or 256-bit keys.
An encrypted hard drive offers the user protection for their data in the event that the hard drive is stolen or accessed by unauthorized users. Without the key or password, the drive and its data are inaccessible. There are many applications that provide encryption for data resident on a storage device or being transmitted across a network. One of these is Microsoft’s BitLocker.
What is BitLocker?
![]() BitLocker is a proprietary encryption program offered by Microsoft on some of its versions of the Windows operating system. It is available to users with:
BitLocker is a proprietary encryption program offered by Microsoft on some of its versions of the Windows operating system. It is available to users with:
- The Ultimate and Enterprise editions of Windows Vista and Windows 7;
- The Pro and Enterprise editions of Windows 8 and 8.1;
- The Pro, Enterprise, and Education editions of Windows 10 installed on their computer.
It is easy to use and can encrypt your hard drive and protect against malware attacking your system’s firmware or attempting to make other unauthorized changes without a noticeable slowdown.
BitLocker System Requirements
In addition to running one of the support flavors of the Windows OS, there are some other system requirements which need to be fulfilled in order to run BitLocker. You are required to have a drive with at least two partitions as well as a special chip known as Trusted Platform Module (TPM). The TPM’s role is to run authentication checks against your system’s software, hardware, and firmware. If the TPM detects unauthorized changes to your system it will boot in restricted mode to thwart possible attackers.
![]() Even without a TPM you can use BitLocker in software mode. For more information on setting up BitLocker we suggest consulting this Microsoft support page.
Even without a TPM you can use BitLocker in software mode. For more information on setting up BitLocker we suggest consulting this Microsoft support page.
BitLocker Password and Security Key
When you are setting up BitLocker there will be a point where you will need to assign a password to be used each time you start your machine. You need to select whether you intend to enter the password manually or by storing it on a USB key. Using the key method poses the risk that the USB key can be lost, leaving you unable to authenticate when booting your computer.
You also need to save a recovery key to protect against issues you may encounter when unlocking your computer. You have several options for saving the key, and you can use as many of them as you wish. It is probably a good idea to use at least two of them. The options are:
 Saving the recovery key to your Microsoft account;
Saving the recovery key to your Microsoft account;- Printing the key;
- Saving the key to a file;
- Saving the key to a flash drive in Windows 10.
Choosing the method in which you store your recovery key entails selecting the type of safety you are most interested in maintaining. Saving the key to your Microsoft account will let you unlock and decrypt your files if you lose the flash drive or the paper on which it was printed. It also poses the risk of someone accessing your Microsoft account and gaining access to the key and thereby your hard drive. We leave it up to you to determine which risk you are more comfortable taking.
What if You Have Forgotten Your BitLocker Password
Let’s say you have a computer which you have protected with BitLocker that has not been used for some time. You go to start it up and cannot remember the password. This is definitely problematic. There is some critical data stored on the drive that you absolutely have to be able to access. What are your options if you cannot unlock your drive normally?
 Attempt access with your usual passwords
Attempt access with your usual passwords
Despite warnings to create unique, strong passwords made up of a combination of alphanumeric and special characters, many users still use simple words or phrases to protect their data and user accounts. Try to relax and remember passwords that you may have used in the past. With some luck, you may stumble onto the correct password and gain entry to your hard drive.
 Perform a BitLocker recovery
Perform a BitLocker recovery
In the event that you cannot access a BitLocker protected drive, you may be called upon to perform a BitLocker recovery. This can be done in a variety of ways.
- The user can type in the 48-digit recovery password.
- A domain administrator can recover the password from Active Directory Domain Services if that is where the password was stored.
- Employ a data recovery agent to unlock the drive. The drive must be mounted as a data drive in order for the agent to unlock it.
Recovery is done through the command line by using the following procedure depending on if you are recovering a local or remote machine.
Forcing recovery on a local machine:
- Click the Start button, type CMD in the Search box.
- Right-click cmd.exe, and then click Run as administrator.
- At the command prompt, type the following command and then press ENTER:
manage-bde -forcerecovery <Volume>
To force recovery for a remote computer:
- On the Start screen, type
cmd.exe, and then click Run as administrator. - At the command prompt, type the following command and then press ENTER:
manage-bde -ComputerName <ComputerName> -forcerecovery <Volume>
 Employ third-party data recovery software
Employ third-party data recovery software
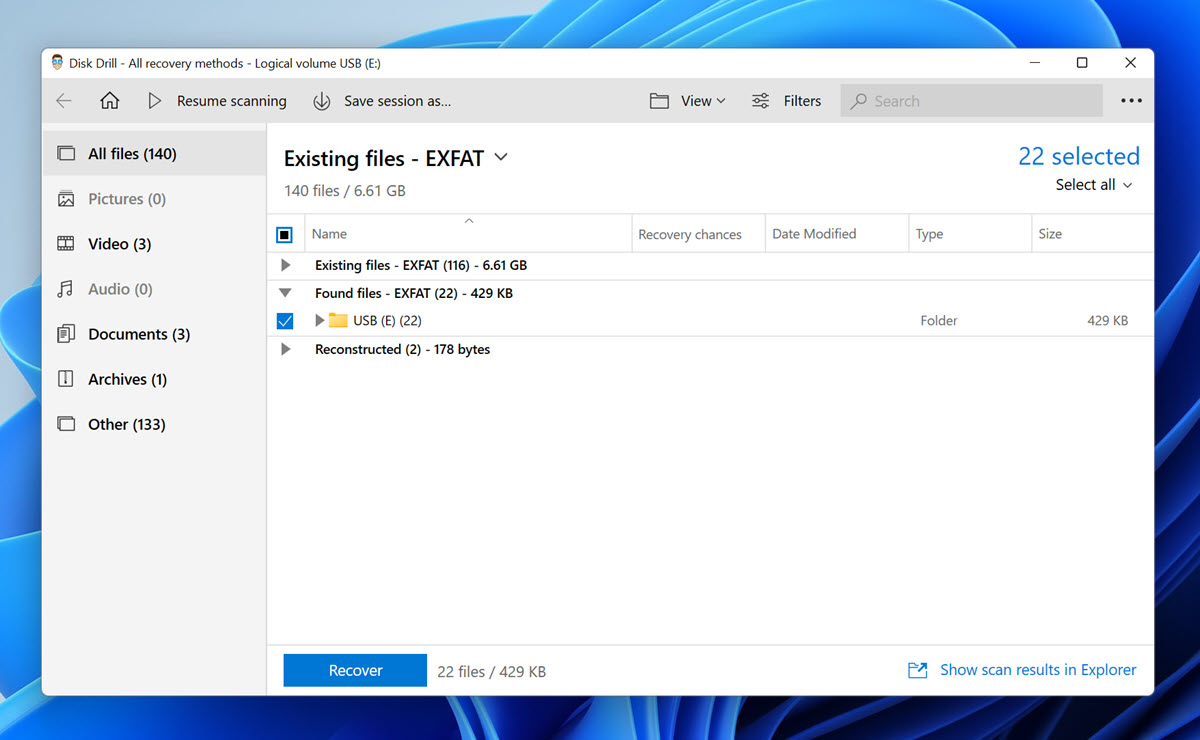
There are data recovery applications available that may be able to extract data from encrypted BitLocker containers. One such tool is Disk Drill for Windows. Version 4 of this app can access files in the BitLocker containers and assist in recovering data from an encrypted drive. This is a more cost-effective method of recovery than sending your disk to a data recovery service, but you will still need to unlock the BitLocker container prior to running Disk Drill.
To recover data from a BitLocker-encrypted drive using Disk Drill:
- Download and install Disk Drill on the computer to which the encrypted drive is connected.
- Launch File Explorer.
- Right-click the encrypted drive.
- Select the Unlock Drive option and enter your BitLocker password.
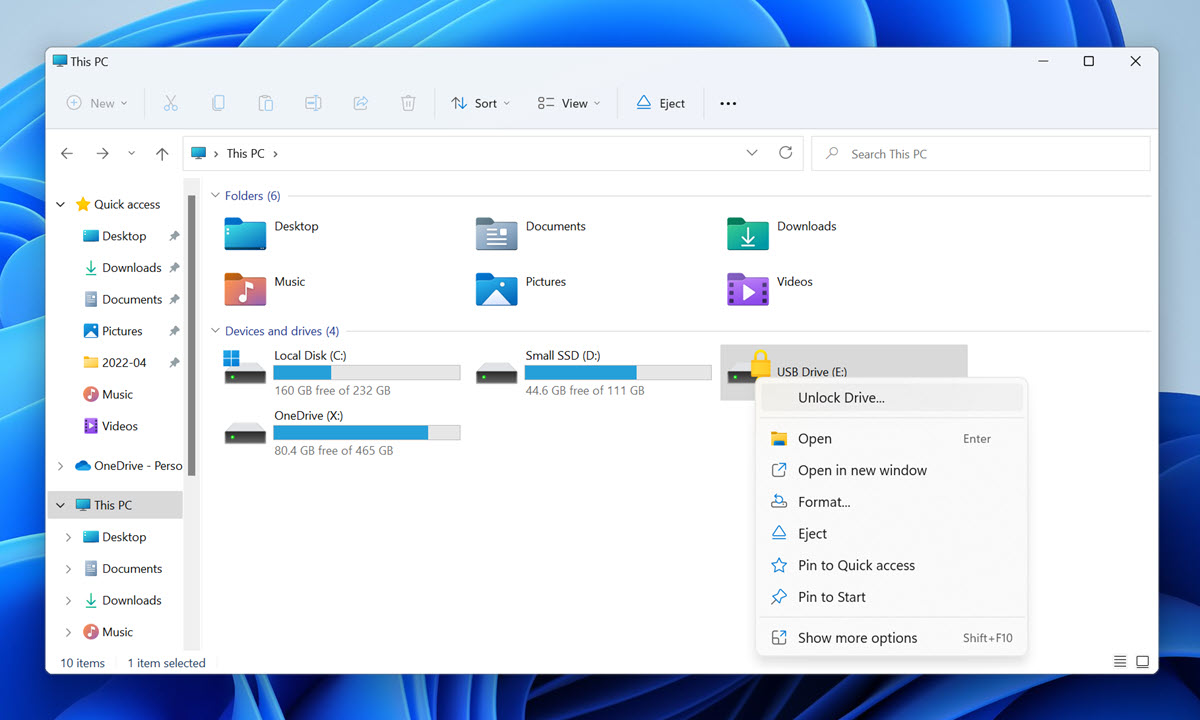
- Launch Disk Drill and scan the encrypted drive. You can also unlock an encrypted drive directly from Disk Drill by selecting the encrypted partition and clicking the Unlock now button. Disk Drill will prompt you to enter your BitLocker password.
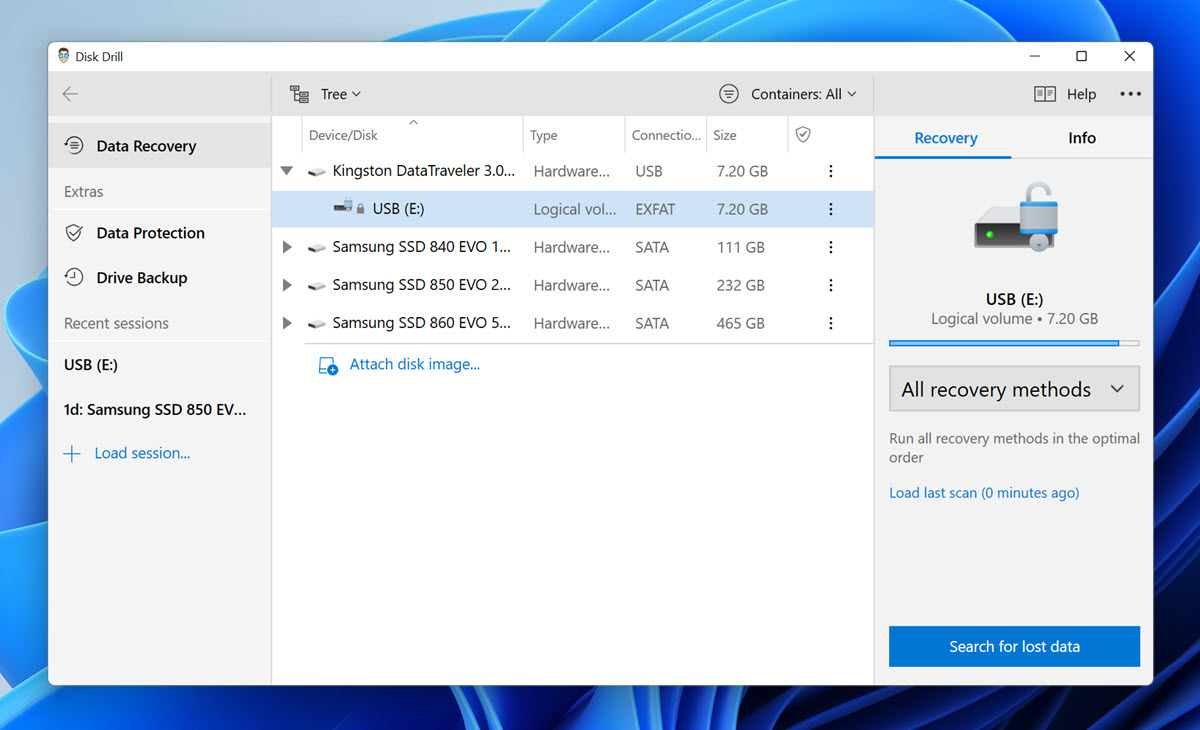
- Analyze the recovery results and select all files you want to recover.
- Click the Recover button and recover the selected files to a safe location.
 Use a Data Recovery service
Use a Data Recovery service
In extreme cases, you may need to remove your hard drive and send it to a data recovery service where they can possibly extract the encrypted data from the device. This will necessitate a financial investment in contracting the service and in purchasing a replacement drive. This will only work if your BitLocker password is not lost, but the storage device is unresponsive. That’s when software-based methods won’t work and the recovery lab may be your best bet.
 Using the BitLocker Repair Tool
Using the BitLocker Repair Tool
 Microsoft has made the BitLocker Repair Tool (Repair-bde) available, and you can use it to access data protected with BitLocker. You should use the tool if the BitLocker recovery methods described above failed to resolve the issue.
Microsoft has made the BitLocker Repair Tool (Repair-bde) available, and you can use it to access data protected with BitLocker. You should use the tool if the BitLocker recovery methods described above failed to resolve the issue.
Using the Repair-bde tool, you can reconstruct critical parts of your encrypted drive to salvage recoverable data from it. In order to use the Repair-bde tool, you need to provide a valid recovery password or recovery key is used to decrypt the data. In situations when the BitLocker metadata data has become corrupt, a backup key package is also necessary.
Here’s an example of how the Repair-bde tool can be used to repair encrypted drive C and write its content to drive D using the correct 48-digit recovery password:
repair-bde C: D: -rp 111111-222222-333333-444444-555555-666666-777777-888888
The parameter -rp tells the Repair-bde tool to use the provided numerical recovery password to unlock the encrypted drive, and it can be also written as recoverypassword.
 Use the BitLocker Encryption Options Application
Use the BitLocker Encryption Options Application
If you’re struggling to access data stored on your BitLocker-encrypted work computer because you don’t remember your PIN or password, then you should look for the recovery key ID in the BitLocker Encryption Options application.
To access this application to retrieve your recovery key:
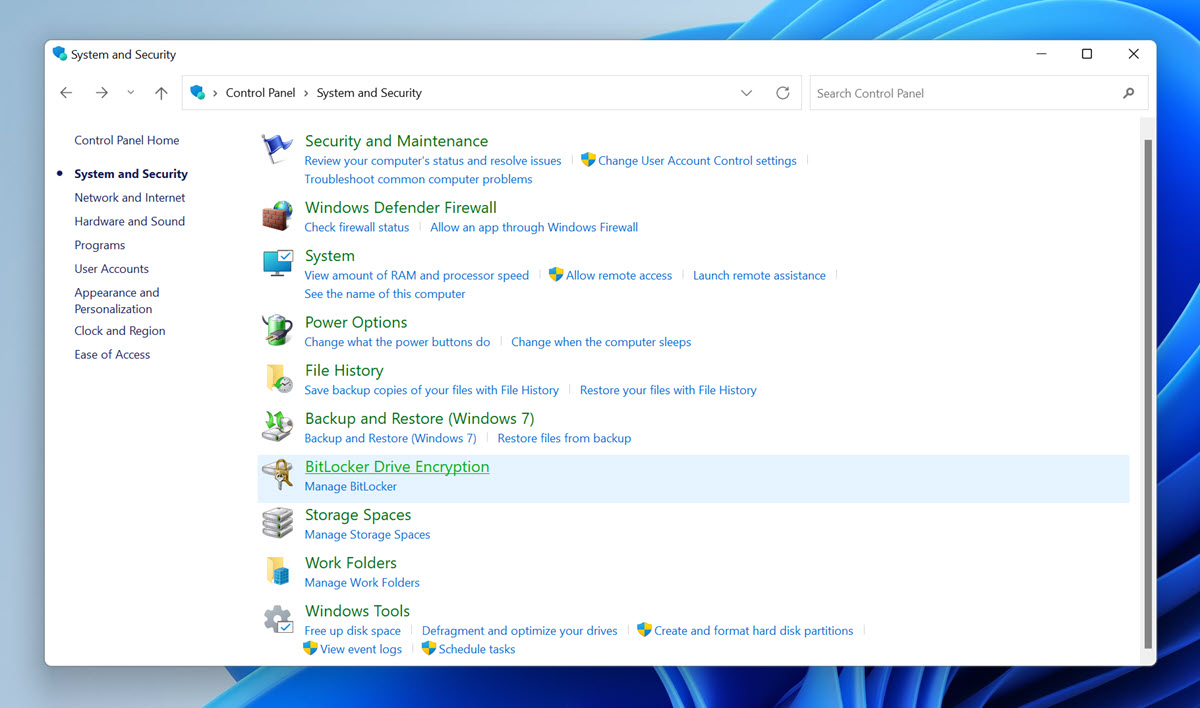
- Open the classic Control Panel.
- Select System and Security.
- Click BitLocker Drive Encryption.
- Select Unlock Drive.
- Click I cannot remember my password.
The BitLocker Encryption Options application should display your recovery key ID, and you can give it to your administrator to unlock your BitLocker-encrypted device.
Resetting Recovery Passwords
The manage-bde command can be used to remove and assign new recovery passwords. You will still need to unlock the BitLocker container. Follow these steps to reset a recovery password.
- Remove the previous recovery password with this command:
manage-bde -protectors -delete <Volume> -type RecoveryPassword
- Add the new recovery password:
manage-bde -protectors –add <Volume> -RecoveryPassword
- Get the id of the new recovery password and copy it down for the next step:
manage-bde -protectors -get <Volume> -Type RecoveryPassword
- Backup the new recovery password to Active Directory Domain Services:
manage-bde -protectors -adbackup <Volume> -id <{EXAMPLE6-5507-4924-AA9E-AFB2EB003692}>
Conclusion
Encrypting any data or device is the best method to employ to protect sensitive information. It can pose a problem if the password used to enact the encryption cannot be recalled when needed. While you certainly don’t want the password available to any prying eyes, you do need to ! ensure that you have a copy in a safe place or are using a password that you will not forget.
FAQ
In that case, you should retrieve your recovery key ID using the BitLocker Encryption Options Control Panel application:
- Open the classic Control Panel and go to Select System and Security.
- Click System and Security and then select the Unlock Drive option.
- Click I cannot remember my password.
You can easily disable BitLocker by formatting the encrypted drive:
- Press Win + X and click the Disk Management option.
- Right-click the encrypted drive and choose the Format option.
- Click OK to begin formatting.